Awesome Security accounts on Mastodon.
 Security
Security
Lisi Hocke
@[email protected]security engineer, holistic tester, quality enabler, agile experimenter, sociotechnical symmathecist, team glue. volleyball player, game lover, story escapist. she/her.
#tech #security #CyberSecurity #SecurityEngineering #ProdSec #AppSec #DevSecOps #testing #quality #development #software #collaboration #pairing #EnsembleProgramming #EnsembleTesting #SoftwareTeaming #agile #experimenting #sociotechnical
Have I Been Pwned
@[email protected]Check if you have an email address or password that has been compromised in a data breach. Created and maintained by @troyhunt
Matt Blaze
@[email protected]Scientist, safecracker, etc. McDevitt Professor of Computer Science and Law at Georgetown. Formerly UPenn, Bell Labs. So-called expert on election security and stuff. https://twitter.com/mattblaze on the Twitter. Slow photographer. Radio nerd. Blogs occasionally at https://www.mattblaze.org/blog . I probably won't see your DM; use something else. He/Him. Uses this wrong.
Jerry 🦙💝🦙
@[email protected]Recovering CISO
May have an orchid problem
Bad photography
Worse dad jokes
The worst Infosec hot takes
Podcast: https://defensivesecurity.org
Blog: https://infosec.engineering
Twitter: @maliciouslink
https://Infosec.Exchange Admin
#infosec #security #cybersecurity #risk #fedi22
…and for fucks sake, be nice to each other. We are only here for a brief time. Make it enjoyable.
To help support the costs associated with running this instance, please consider donating. You can set up recurring donations here:
Patreon: https://www.patreon.com/infosecexchange
Ko-Fi: https://ko-fi.com/infosecexchange
Liberapay: https://liberapay.com/Infosec.exchange/
BuyMeACoffee: https://buymeacoffee.com/infosecexchange
You can also support with a one-time donation using PayPal to "[email protected]".
Manuel 'HonkHase' Atug
@[email protected]20yrs Sec #CCC, Geraffel native, c-base, AG KRITIS, CSCB, #AGND #hacking, #Ethik, #KRITIS, OT & IT-Security, working at HiSolutions, http://Threema.id/X9H873XJ
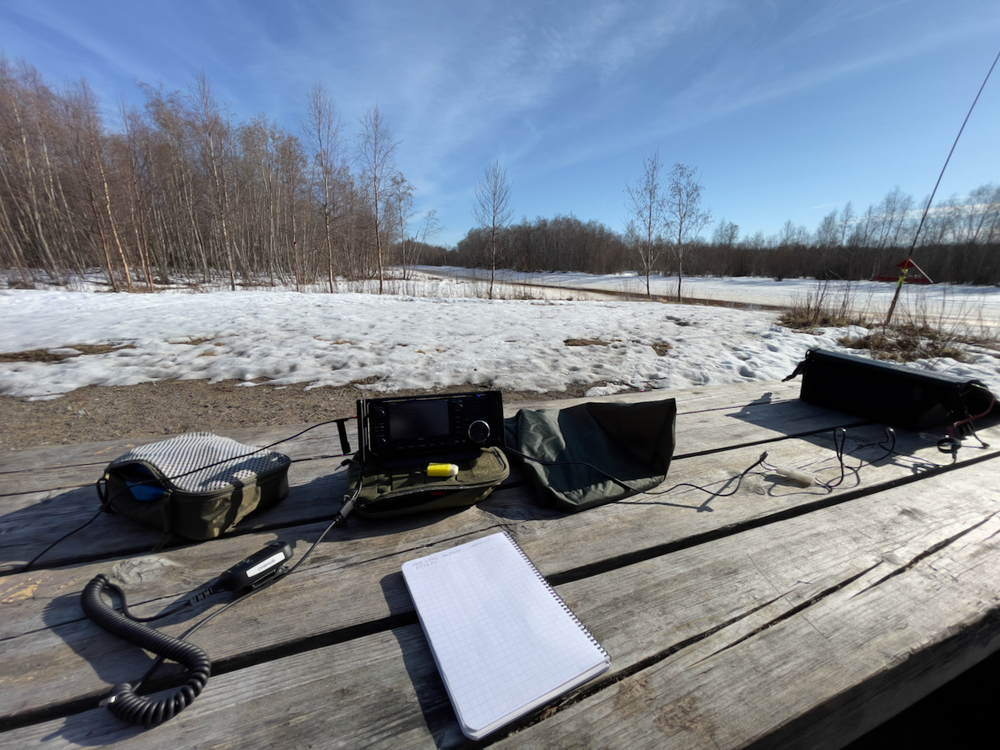
Ossi OH8HUB
@[email protected]On nights I'm a hacker and licensed #HamRadio op since 1999. Currently learning about #HF and #digimode (#ft8, #js8call, #vara). I try to do #pota and #wwff activations whenever possible.
On days I'm co-founder and R&D lead (#rustlang) on cybersecurity startup.
VessOnSecurity
@[email protected]Anti-virus, malware and infosec expert, crypto amateur, privacy advocate and general annoyance.
PGP keyID: 0x365697c632dd98d9
Devon Maloney
@[email protected]Security Engineering and Architecture at Apple. Vulnerability research. Embedded systems in Swift. Alumnus RPISEC. Previously ReSwitched team. 🏳️🌈
Harry Sintonen
@[email protected]Infosec consultant at REVƎЯSEC https://reversec.com - Coding, Research + various other interests
SteamDB
@[email protected]👀 Tracking all things Valve and Steam.
ℹ️ We are not affiliated with Valve in any way.
Otto Sulin
@[email protected]Information security, open source and all things outdoors 🇪🇺
The Calyx Institute
@[email protected]Our mission is to educate the public about privacy in digital communications and to develop tools that anyone can use. By embracing "privacy by design," we help make digital security and privacy more accessible to everyone. Help support our nonprofit mission-- become a member and get a hotspot with unlimited wifi or a phone with CalyxOS! https://members.calyxinstitute.org/enroll/membership
Davi Ottenheimer
@[email protected]flyingpenguin.com since 1995.
Gebrüder Ottenheimer since 1862.
History of security, security of history.
Ian Campbell 🏴
@[email protected]Security ops engineer for DomainTools, DT Investigations threat researcher, writer, voracious reader. he/him. Fan of good trouble. Opinions here mine only. No LLM content from me, all flaws detected are human-generated. Autistic/depressed/anxious/hungry.
#infosec #cybersecurity #privacy #actuallyautistic #neurodivergent
Troy Hunt
@[email protected]Creator of @haveibeenpwned. Microsoft Regional Director and MVP. Pluralsight author. Online security, technology and “The Cloud”. Australian.
 Shlee booped around &
Shlee booped around &
@[email protected]
Teacher, Mother, Lover. Says good morning in the evening! Join your union!
Admin of aus.social & techhub.social. Direct action charity founder. Cloud/Cybersecurity/Infosec engineer.
(any toots should not be used as evidence of crimes, and all confessions are jokes)
░M░Y░S░E░R░V░E░R░I░N░D░C░
Kuketz-Blog 🛡
@[email protected]Kuketz-Blog: Gegen Überwachungskapitalismus ✊
Datenschutz, IT-Sicherheit und digitale Selbstbestimmung – kritisch, unabhängig und spendenfinanziert.
#Sicherheit | #Datenschutz | #Hacking | #Security | #Privacy | #Infosec | #DSGVO | #Netzpolitik | #Karlsruhe
Hier schreibt die Redaktion des Kuketz-Blogs:
/kuk @kuketz
/meb @rufposten
/lax @lacrosse
Hilfe & Support: https://www.kuketz-forum.de/
Impressum: https://www.kuketz-blog.de/impressum/
Toots werden nach 2 Jahren gelöscht ✅
Josh Bressers
@[email protected]VP of Security at Anchore - Podcaster (http://opensourcesecuritypodcast.com http://hackerhistory.com) - Blogger (http://opensourcesecurity.io) - He/Him
Johnny Xmas
@[email protected]Attractive nuisance | 3rd Gen Hacker | BurbSec | OT\ICS | Seen on Fox, Wired, TechCrunch… | Infosec’s Community Builder | I only have time to do great things.
heise Security
@[email protected]News und Hintergrund-Geschichten von heise Security - dem Sicherheitsportal von heise online.
Offizieller Account
🤖 Die meisten Posts sind automatisiert
CosicBe
@[email protected]COSIC provides a broad expertise in digital security and strives for innovative security solutions.
COSIC is headed by Bart Preneel.
Computer Security and Industrial Cryptography group
https://www.esat.kuleuven.be/cosic/